Step‑by‑Step Guide to Harvest-Now-Decrypt-Later (HNDL) Protection with Layer 2 Encryption
Mitigating Harvest-Now-Decrypt-Later (HNDL) Threats
Organizations in data-sensitive industries, such as government, defence and intelligence, need to mitigate HNDL threats today. This is because a bad actor can collect network traffic (encrypted or otherwise) today, and use a quantum computer in the near future to read its contents.
Most solutions rely heavily on IP Layer (Layer 3) encryption, such as TLS and IPsec, or application‑layer (Layer 7) encryption. While these encryption approaches protect data payloads, they often leave network metadata exposed, including IP addresses, ports, and protocol information. Attackers can use this metadata for profiling, reconnaissance, or traffic analysis.
Layer 2 encryption is another approach to mitigating HNDL threats. It further closes the metadata gap by encrypting everything carried over the link, including:
- Source and destination IP addresses
- VLAN tags
- Protocol headers
- Payload data
This creates a fully private, network tunnel that hides both the data and its context.
What Makes a High-Speed Encryptor Quantum-Safe
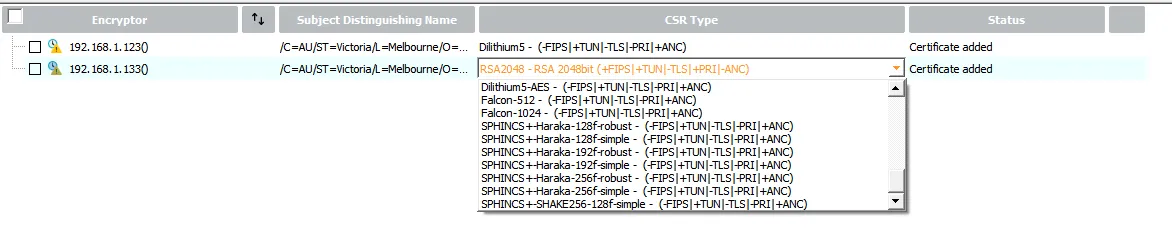
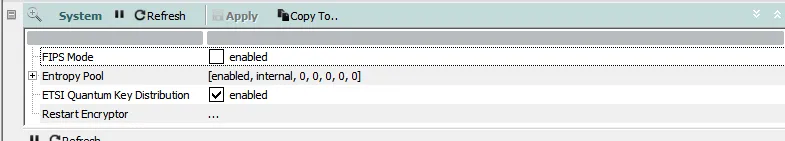
Network encryptors perform Layer 2 encryption and the high-speed variants are typically known as high-speed encryptors (HSEs). HSEs that support post-quantum cryptography, designed to resist attacks from future quantum computers (for both digital signing and key establishment), can achieve quantum-safe network traffic protection. One example of a quantum-safe HSE is the Thales CN-series network encryptor, which supports quantum-safe digital signature algorithms (see Fig. 1 below) and even Quantum Key Distribution (see Fig. 2 below).
When deployed at Layer 2, HSE provides:
- End‑to‑end confidentiality across the entire link
- Line‑rate encryption with negligible performance impact
- Future‑proof protection against both classical and quantum attacks
- Transparent operation, requiring zero changes to existing IP networks
How to Set up and Verify the Protection
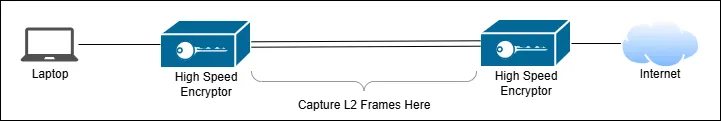
To illustrate the impact of Layer 2 HSE encryption, we use PacketQC by pQCee, a network ACDI (Automated Cryptography Discovery and Inventory) tool that scans a network capture and visually displays the quantum-security assessment of network data in the capture. PacketQC allows us to monitor network protocol headers, identify IP information, and observe changes across network captures, making it ideal for demonstrating how traffic looks before and after encryption.
In our setup, we have a user accessing several websites, including github.com and dbs.com.sg, over the Internet. We use PacketQC to examine the network traffic first and then once more after enabling HSE Layer 2 encryption (see Fig. 3 above).
Normal Network Traffic (Before)
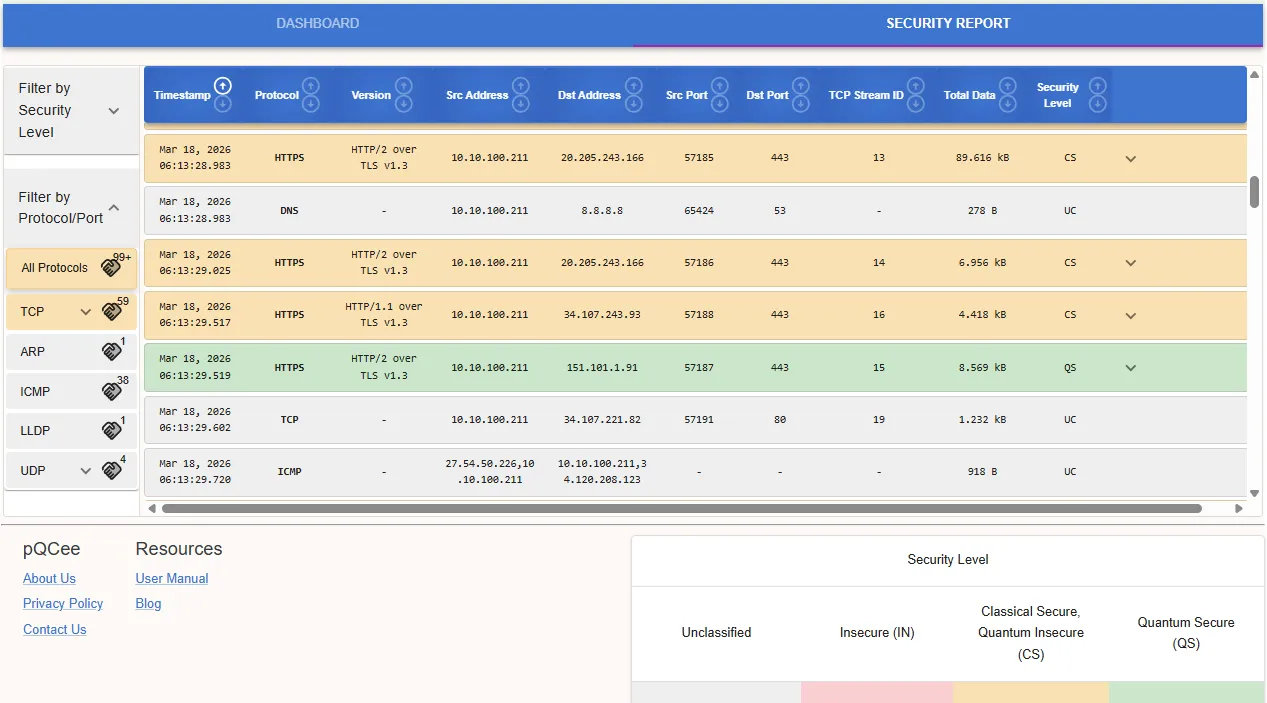
We upload the first PCAP file to PacketQC, click "Generate Network Report" and view "Security Report" tab to inspect the network traffic without Layer 2 encryption. In Fig. 4 above, PacketQC is able to view the network metadata (including IP addresses, protocol types, port numbers, and traffic patterns). The yellow-colored connections indicate that PacketQC has identified some HTTPS connections that are not quantum-safe. These connections are susceptible to Harvest-Now-Decrypt-Later attacks.
In this first network capture, we observe that even if payloads are encrypted at higher layers, a lot of network metadata remains exposed. This metadata can reveal who is communicating, which services are in use, and how traffic flows across the network.
Network Traffic with Layer 2 Encryption Enabled
We repeat the same test now with HSE Layer 2 encryption enabled.
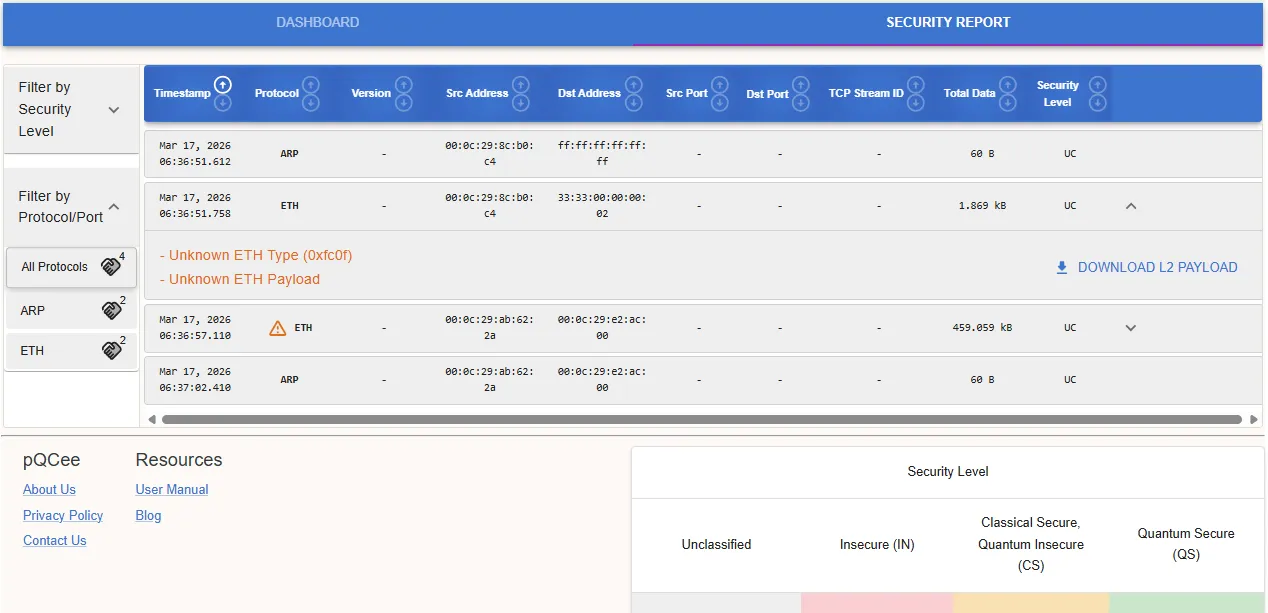
We upload the second PCAP file to PacketQC and perform the same steps as described earlier. In Fig. 5 above, PacketQC is unable to extract meaningful network metadata, and it allows the user to download the encrypted Layer 2 payload for further detailed verification.
In this second network capture, we observe that all network traffic appears as encrypted frames. Network metadata is concealed, traffic patterns are obscured, and the link effectively becomes an opaque, quantum‑safe channel. With Layer 2 encryption in place, both data and metadata are protected, providing comprehensive confidentiality against present and future threats, including those posed by quantum‑capable adversaries.
Key Takeaways
As organisations move toward a quantum‑resilient future, securing the full breadth of network information becomes essential. Layer 2 encryption with quantum-safe HSEs offers an elegant and effective solution by protecting everything that traverses the link, not just payloads, but metadata as well.
The combination of pQCee PacketQC plus Thales CN-series network encryptor runs a post-quantum migration project through the discovery (using PacketQC) + mitigation (using the Thales HSE) + validation (using PacketQC) phases, making it an end-to-end solution. From a user's standpoint, the migration is seamless and does not impact the customer experience (CX). From a security perspective, we can clearly observe the difference between unencrypted and Layer 2 encrypted traffic. The transformation is profound: sensitive Internet Protocol (IP) information that once travelled in plaintext becomes fully protected, giving enterprises confidence that their networks are secure now and in a post‑quantum future.
The following organizations participated in the pilot trial:
- Thales, for the use the HSE Layer 2 encryptors
- pQCee, for the use of PacketQC
- Pacific Tech, for providing the resources and technical engineering expertise in running the trial
Author
Nicholas Ho
Nicholas seriously enjoys learning new knowledge. He is so serious about it that his hobby is to collect hobbies. His most enduring hobby, since 1997, is to continuously explore the ever-evolving domains of applied cryptography, software development, and cybersecurity. His latest aspiration is to add the word quantum in front of each of these 3 domains. Nicholas is currently a Senior Cryptographic Engineer at pQCee.com. Akin to many Singaporeans, he also enjoys collecting popular certifications, including a CS degree, an Infocomm Security masters, CISSP, and CISA.